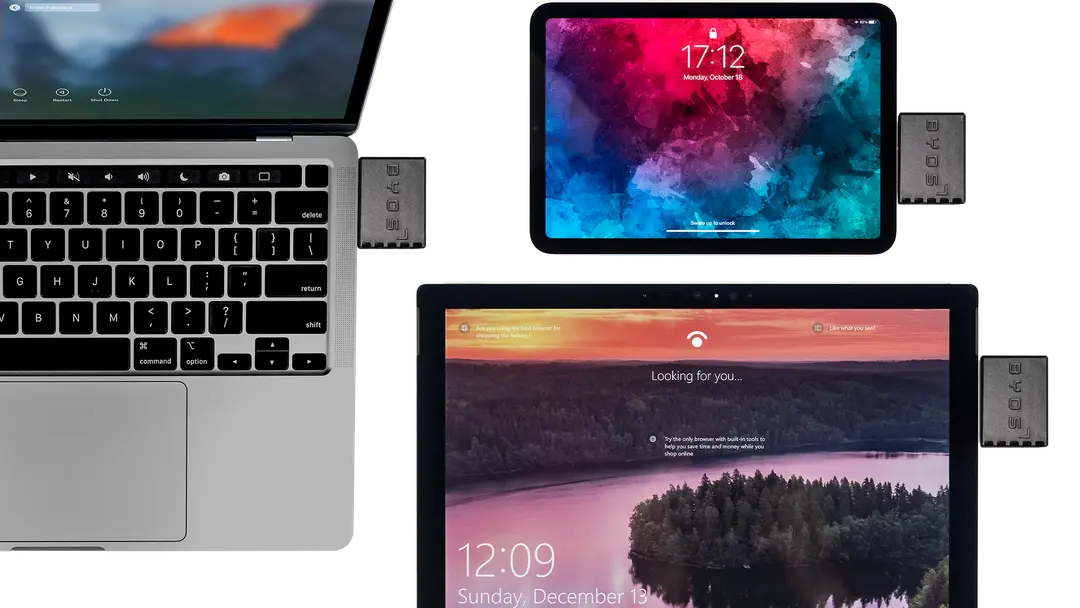
🚀 Byos Secure Embedded Edge - Back-Ordered: Reserve Yours Today
Byos Bug Bounty Program
As part of Byos’ commitment to security, we reward researchers who share with us critical issues and the techniques used to exploit them. We make it a priority to resolve confirmed issues as quickly as possible in order to best protect customers.
The Apple© iPad® and MacBook® Pro are trademarks of Apple Inc. The Microsoft© Surface Pro® is trademark of Microsoft Corp.
Eligibility
Any researcher who has purchased a Secure Edge device is eligible to participate in the Byos Bug Bounty Program.
Bounty Categories
The Byos Bug Bounty is split in 4 levels, according to different bug categories:
-
Low (XSS, CSRF, RFI, broken Web features)
-
Medium (Stored XSS, SSRF, LFI, DDoS)
-
High (IDOR, SSRF, Auth Bypass, Breaking the Encryption layer)
-
Critical (RCE, IDOR, SSRF, SQLi, Core Protection Mechanism Bypass)
Submitting Vulnerability Disclosure Reports
Vulnerability Disclosure Reports need to describe the weakness or the type of potential issue discovered, in full detail.
The report should include the following components:
-
A description of the proof of concept
-
The nature and classification of the vulnerability, including the severity in the opinion of the researcher
-
The steps required to reproduce the vulnerability
-
What the potential implications for the company, if an attacker were to exploit the vulnerability
-
A demo of the method, including but not limited to screenshots and videos.
Disclosure
-
There is a strict non-disclosure of vulnerabilities found for a period of 90 days (known as the Lockdown Period). If new vulnerabilities are found post Lockdown period, these do not fall under the coverage of the Bug Bounty. Researchers are encouraged to report all vulnerabilities post-Lockdown period and will be compensated appropriately.
-
If the source code is discovered during the Bug Bounty, no public disclosure is permitted. The researcher must only disclose the method used to Byos.
-
Any actions to intentionally harm or break the device are forbidden.
-
The scope of the Bug Bounty Program is restricted to: the Secure Edge Devices, the Management Console, or any other cloud server within our service offering.
-
By participating in the Byos Bug Bounty and submitting all findings, the researcher does not have the right to claim the vulnerability later in time. The content, intellectual property, copyright, and ownership belongs to Byos, Inc.
-
Vulnerability Disclosure Reports must be clear and reproducible.
-
All vulnerabilities found must be reported.
To claim a bug bounty, please email your Vulnerability Disclosure Report to support [at] byos.io