🚀 New Byos Secure Embedded Edge in pre-order! Join the waitlist
CISOs’ 12 Biggest Network Security Challenges
CISO | Network | Data Breach
July 17th, 2023
CISOs have enough on their plates with threats growing more sophisticated, more evasive, more pervasive, more persistent, and more diverse. IoT, remote work, mobile, BYOD, and cloud add to the challenges that we now recognize as the “extended enterprise”. Add to all these factors, the pace of technology change and digital transformation complicate the CISO’s job.
To gain a better understanding of the network security challenges CISOs face, Byos interviewed 100 security leaders in large commercial and governmental organizations. These CISOs shared their experiences, challenges and invaluable insights into the issues they face.
Since Byos is a network/endpoint security company, our discussions focused on the four main challenges (which emerged early in our interviews), related to network and endpoint security.
Challenges: Accessibility, Availability, Security and Control
Within each category, we discovered pain points, generally speaking, that CISOs want to address.
Conventional Wisdom Leads into a New Mindset
For many years, the conventional wisdom has been that increasing security comes at the expense of usability, convenience, and simplicity. However, with advancements in technology and methodologies over the last few years, we are finding that - when done with innovative thinking, proper design, a user engagement - CISOs can reduce “friction” and create business enablers at the same time as reducing risk.
An excellent example of this is digital signatures, which not only reduced fraud and secured documents, but also streamlined processes, and created significant savings in time (document reviews, faxing, and filing), commodities (paper and storage), and expenses (printing and postage). It was quickly adopted by most industries, with the obvious exception of healthcare, and has become a preferred means of facilitating document exchanges.
Setting the Stage
The insights gained from our research can help you identify areas of improvement and create strategies that align with your o goals. We encourage you to continue to share your experiences and insight with us as we make progress with methodologies and technologies. Together, we can improve your risk profile in an ever-changing threat landscape while pointing to how you are improving business outcomes.
Using the digital signature experience as a model, a primary goal of this research was to begin the process of addressing network security from the perspective of reducing “friction” and finding ways that network security can be a business enabler rather than a business inhibitor.
These challenges are complex, interrelated, and require a multi-pronged approach that blends a balance of technology, policy, and culture. By incorporating the solutions proposed in this report, enterprise cybersecurity teams will rethink some of their most fundamental assumptions, and find new ways to approach both strategy and tactics.
Here's our findings:
Overall Challenges
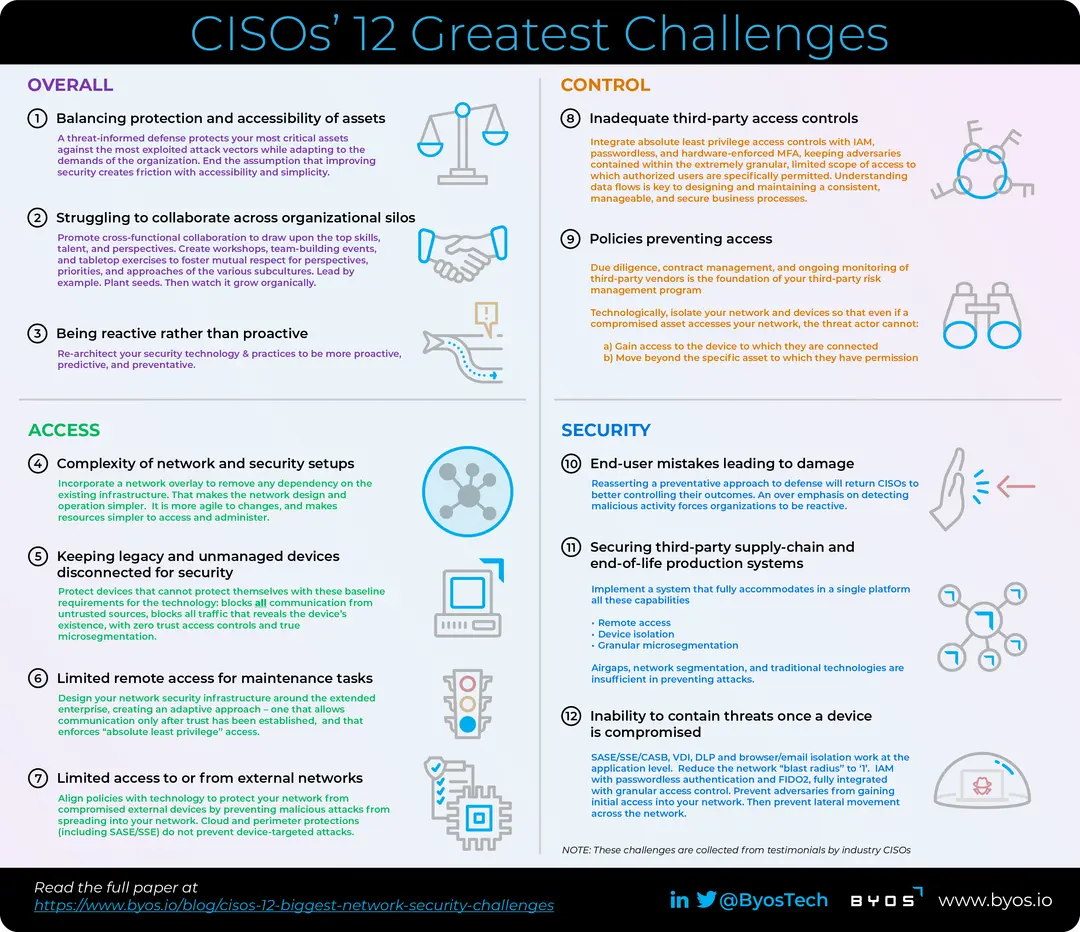
1) Balancing protection and accessibility of assets 2) Struggling to collaborate across organizational silos 3) Being reactive rather than proactive
Root Cause
Protecting assets is a top priority, but we must balance between protecting them vs. making them more accessible to employees, customers, and partners. This can create tensions between the security team and other parts of the organization, who may feel that security measures are impeding their ability to work efficiently.
Cybersecurity, IT/Infrastructure, OT, and other security participants impact everyone in the cybersecurity apparatus. We need more cohesiveness in our strategies, operations, culture, and priorities. That will result in better efficiencies and effectiveness.
CISOs feel like they are always on the defensive, reacting to new threats and unanticipated changes in the business. It is critical to become more proactive in anticipating, mitigating, and preventing attacks before they occur.
Forward-Looking Mindset
Adopt a threat-informed defense methodology that protects your most critical assets against the most exploited attack vectors while adapting to the demands of different parts of the organization. Find ways that end the assumption that improving security creates friction with accessibility and simplicity .
Promote cross-functional collaboration to draw upon the top skills, talent, and perspectives from each group. Create workshops, team-building events, and tabletop exercises that foster mutual respect for the perspectives, priorities, and approaches of the various subcultures in the enterprise. Lead by example, plant the seeds. Then watch it grow organically – from the ground up.
Re-architect your security technology & practices to be more proactive, predictive, and preventative.
CISO Insight
“I feel like I’m always waiting for the next shoe to drop.” "It’s a tough place to be in. We can't block, airgap, or isolate every asset and then expect people to get their jobs done. On the other hand, we can’t allow an Equifax or Target event, or be forced into a situation requiring a Colonial Pipeline kind of decision.”
Byos Tip: The MITRE framework moves you from a “controls & gaps-based model” toward one that focuses on the techniques and attack flows that adversaries exploit the most. For a simple illustration of how you can focus your attention and spend where it will be more effective, have your security architect brief you on this article, “Prevent Attackers from Gaining Initial Access to Your Network”.
Challenges in Accessibility/Availability
4) Complexity of network and security setups
5) Keeping legacy and unmanaged devices disconnected for security
6) Limited remote access for maintenance tasks
7) Limited access to or from external networks
Root Cause
Broad, inconsistent, and complex network and security infrastructures limit how quickly our business can adapt and transform. Establishing simple, secure, and consistent access is critical to centralizing administration and data collection
We are forced to isolate, segment, or keep legacy and unmanageable devices disconnected so they are not exposed. That limits how assets and information can be accessed, administered, and maintained. | Protect devices that cannot protect themselves with these baseline requirements for the technology: blocks all communication from untrusted sources, blocks all traffic that reveals the device’s existence, with zero trust access controls and true microsegmentation.
Normal maintenance, troubleshooting, maintenance, and support activities require onsite access because security policies & procedures prohibit remote access. Additional cost, delays, and complicated processes result.
Traditional protections are ineffective in opening access to/from assets or networks outside the organization’s control. The result is reduced accessibility and availability of critical assets.
Forward-Looking Mindset
Incorporate a network overlay to remove any dependency on the existing infrastructure. The benefits are that the network design and operation are simpler. It is flexible as changes happen, makes resources simpler to access and administer.
Design your network security infrastructure around the extended enterprise, creating an adaptive approach – one that allows communication only after trust has been established, and that enforces “absolute least privilege” access.
Align policies with technology to protect your network from compromised external devices by preventing malicious attacks from spreading into your network. cloud and perimeter protections (including SASE/SSE) do not prevent device-targeted attacks.
CISO Insight
"Sometimes I get this feeling when I’m walking into a meeting with my executive leadership or the operations directors, that there is this predisposed assumption that I’m going to introduce roadblocks to their pet project they are excited about – like ‘here comes the cloud that’s going to rain on my parade’.”
Byos Tip: Operationalizing network security architectures in the past required extensive infrastructure upgrades, redesigns, planning, integration, complex phased project plans, and long deployment cycles. Today, network technology can begin with two devices, scaling to an international, enterprise deployment over existing, diverse networks without any changes. To learn more about Byos’ “2 devices, 2 hours, 2 success” program, contact us now.
Control Challenges
8) Inadequate third-party access controls
9) Policies preventing access
Root Cause
Access controls for BYOD, WfA/remote, and IT/OT interactions are inadequate for protecting our assets from internal and external threats.
Policies & risk prevent us from allowing access from devices and networks we don’t control, as well as those within our control that are extremely complex
Forward-Looking Mindset
Integrate absolute least privilege access controls with IAM, passwordless, and hardware-enforced MFA. Your objective is to keep adversaries contained within the extremely granular, limited scope of access to which authorized users are specifically permitted. Understanding data flows is a key factor in designing and maintaining a consistent, manageable, and secure enablement of business processes.
Due diligence, contract management, and ongoing monitoring of third-party vendors is the foundation of your third-party risk management program Technologically, isolate your network and devices so that even if a compromised asset accesses your network, the threat actor cannot
- Gain access to the device to which they are connected
- Move beyond the specific asset to which they have permission
CISO Insight
"We need to have more control and auditability over who has access to our assets, but we also need to be able to support our extended enterprise, regardless of where they are.”
Byos Tip: “Configuration Drift” is a common term used in data centers – but it is applicable to access control administration as well. The result is an accumulation of rule, policy, and configuration changes due to ad hoc deviations and inconsistent day-to-day administration. These changes create gaps that adversaries can exploit and difficulties auditing the current state versus their intended design. Designing the administrative UX in concert with a well-orchestrated process flow creates an environment where “configuration drift” is kept to an absolute minimum.
Security Challenges
10) End-user mistakes leading to damage
11) Securing third-party supply-chain and end-of-life production systems
12) Inability to contain threats once a device is compromised
Root Cause
Despite cybersecurity training, end-users make mistakes that lead to significant damage. We need to find better ways to prevent the inevitable consequences of human error.
Vulnerabilities in third-party devices open threats that were previously resolved. Lack of visibility into the practices of third-parties or a lack of control over their devices are difficult to overcome. Similarly, securing production systems that reach their end-of-support lifecycle faster than the business can replace them. It’s a significant challenge. The result is security gaps, potential vulnerabilities, and “low dangling fruit” for adversaries.
Once a single device is compromised, it is difficult to contain the threat and prevent it from spreading. The potential for damage expands at a rate greater than the number of devices affected.
Forward-Looking Mindset
An over emphasis on detecting malicious activity forces organizations to be reactive. Reasserting a preventative approach to defense will return CISOs to better controlling their outcomes.
Airgaps, network segmentation, and traditional technologies have proven to be insufficient to prevent attacks. Implement a system that fully accommodates in a single platform all these capabilities
-
Remote Access
-
device isolation
-
granular microsegmentation
SASE/SSE/CASB, VDI, DLP and browser/email isolation address this challenge at the application level. IAM with passwordless authentication and FIDO2, fully integrated with granular access controls addresses access trust. Complete your defense with technology that prevents adversaries from initially accessing devices & operating systems, and then prevent lateral movement across the network. That reduces the “blast radius” of a compromise to one asset.
CISO Insight
"We need to find a way to address the human element of security. No matter how much training we provide, there will always be mistakes. We are creating a security-first culture and we’ve been promoting that within IT, in our agile processes, and across the entire enterprise. Now we’re beginning that process with our suppliers and customers. And that requires us to look at our own attitudes. We have abandoned the idea that our users are our last line of defense. We’re taking on the challenge that humans are never going to be 100% foolproof. It’s our job to protect them, not blame them.”
Byos Tip: If a vulnerability can't be exploited from the network or if a backdoor can't be reached, does it need to be patched with the same urgency? Do assets need to be unplugged or decommissioned to avoid exposure?
Conclusion
The challenges faced by CISOs in creating your network security and accessibility strategy can be viewed through the lens of how adversaries build their attack campaigns to maximize your goals and/or effect the most damage possible. By understanding the attack vectors and solutions that address each challenge, CISOs can better defend against these campaigns and protect your assets.
By updating our mindsets to adopting more proactive and preventative approaches to protecting network communication across the extended enterprise, you can improve your defense against adversaries’ attack campaigns and add value by reducing complexity for end-users, accelerating digital transformation initiatives, and opening new opportunities for efficiency and effectiveness.
To learn more about how Byos can help you achieve your goal of preventing your adversaries from reaching their goals, connect with us on LinkedIn or use the button below to start a conversation.
Platform
Use Cases (Industry)
Use Cases (Application)
Patented Technology. © Byos Inc. - Ashburn, VA. - All rights reserved. Byos Secure Edge™ hardware is manufactured in the USA, with a certified supply chain of components. FIPS 140-2 Validated (#4946)